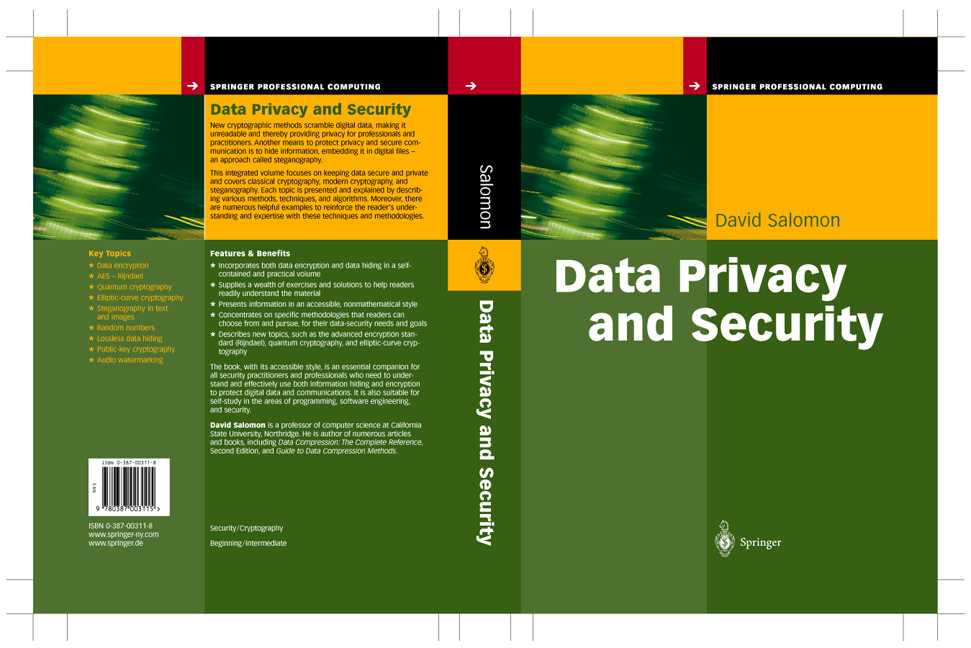
By David Salomon. Published by Springer Verlag May 2003. ISBN 0-387-00311-8. LCCN QA76.9.A25S65 2003. xii+470 pages.
A BibTeX style file and an Errata list are available.
Both classical (paper and pen) and modern (computer-based) cryptographical methods are described. A large part of the book is devoted to steganography, the art and science of hiding information. Again, older methods as well as modern, computer-based methods are included.
Preface vii Introduction 1 Part I Data Encryption 19 1 Monoalphabetic Substitution Ciphers 21 2 Transposition Ciphers 39 3 Polyalphabetic Substitution Ciphers 59 4 Random Numbers 91 5 The Enigma 107 6 Stream Ciphers 131 7 Block Ciphers 155 8 Public-Key Cryptography 195 9 Quantum Cryptography 235 Part II Data Hiding 243 10 Data Hiding in Text 245 11 Data Hiding in Images 269 12 Data Hiding: Other Methods 339 Part III Essential Resources 367 Appendixes A Convolution 369 B Hashing 377 C Cyclic Redundancy Codes 383 D Galois Fields 387 Answers to Exercises 401 Cryptography Timeline 419 Glossary 429 Bibliography 441 Index 453
This section contains extra material added by the author from time to time. These documents add new material or shed new light on material already included in the book.
1. Secure Socket Layer (SSL) is an important protocol used for secure communications on the Internet. Private information should be encrypted before it is transmitted on the Internet. The encryption algorithm is known and security is obtained by the key. Each data transmission uses a different key, selected at random, and the SSL protocol is applied to securely communicate the key over an unsecure communications line. This short document (PDF, 9 pages, 308K) explains the process in detail (thanks to Stephen Fuld for corrections). It also includes a description of the MD5 hashing algorithm.
2. The Enigma cipher machine and the breaking of its code are described in the book in detail. Recent news about advanced Enigma codes were published in http://news.bbc.co.uk/2/low/technology/4763854.stm on 2 March 2006 and are available here, for the readers' convenience, in PDF format.
3. Hedy Lamarr and the invention of spread spectrum technology are mentioned on page 297. Richard Rhodes has written a nice, detailed book titled Hedy's Folly: The Life and Breakthrough Inventions of Hedy Lamarr, the Most Beautiful Woman in the World (published by Doubleday in November 2011). The book describes the lives of Hedy and her coinventor George Antheil, as well as the background and principles of their invention.
4. (May 2017) Page 257 describes a simple proposal for semantic steganography. A somewhat similar approach, proposed and implemented in Python by Mok-Kong Shen, has recently come to my attention. It is freely available here.
5. Appendix A discusses the term "convolution." A better explanation, with examples, of this important term can be found here.
Last Updated 5 May 2017.